From medical devices and industrial equipment to smart home appliances — all are powered by embedded systems. And as these systems become more connected, they become more vulnerable to a wider range of risks.
Discover the most common security vulnerabilities in embedded systems, the real cost of ignoring them, and practical, budget-friendly strategies to protect both hardware and software from emerging threats.
What is embedded system security?
Embedded systems security refers to concepts and techniques that aim to protect software and hardware components from malicious actions and unauthorized data access. Based on the CIA principle, which stands for confidentiality, integrity, and availability, it is meant to safeguard your embedded solution at both the hardware and software levels.
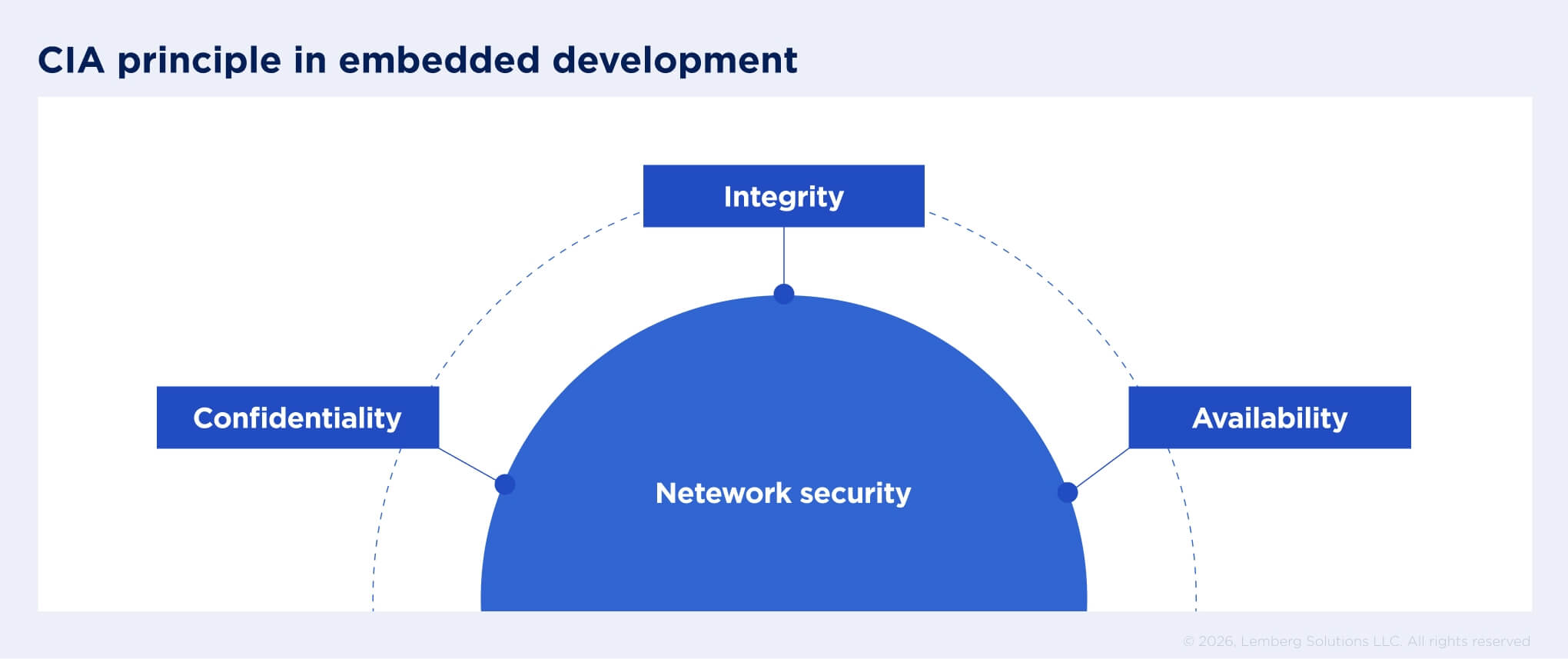
- Confidentiality mandates that only authorized parties can access data on your network, ensuring that encrypted information is transmitted through secure communication protocols.
- Integrity ensures that data-related system operations are reliable and executed as expected.
- Availability responsible for ensuring that authorized users have uninterrupted access to system data, preventing data breaches.
The importance of embedded systems security — and the cost of ignoring
For years, security in embedded systems was treated as good practice, not a necessity. Now, however, the industry views it as one of the most important components of connected devices. So essential that products that are not secure by design cannot legally enter the market.
For example, in the United States, embedded device security is shaped by frameworks developed by the National Institute of Standards and Technology (NIST). By this, we mean the NIST Cybersecurity Framework and related publications such as NIST SP 800-53 and NIST SP 800-193 (Platform Firmware Resiliency Guidelines). At their core, these frameworks emphasize building devices with a Root of Trust that follows a continuous “Protect, detect, and recover” security model. It ensures that even if a device is compromised, its integrity can be restored to a previous safe condition.
For some sectors, these frameworks are no longer voluntary. For instance, the IoT Cybersecurity Improvement Act strictly prohibits U.S. federal agencies from buying any embedded product that cannot meet NIST baselines.
Furthermore, in 2026, the U.S. expects the launch of the Cyber Trust Mark — a new label for wireless consumer goods that comply with NIST IR 8425. Participation is currently voluntary, but for manufacturers, this label has become a requirement for retail placement and brand trust, highlighting that a device matches all "secure-by-design" principles.

In the European Union, embedded products also face additional security regulations. The recent EU Cyber Resilience Act introduces mandatory cybersecurity requirements for products with digital elements, including embedded devices and IoT systems.
For manufacturers, this means embedded security must be integrated from the earliest stages of development rather than added after deployment. Also, the regulation demands a strict vulnerability management process. Manufacturers must report system vulnerabilities within 24 hours and maintain security updates throughout the device lifecycle. Failure to follow the requirements leads to fines of up to 2.5% of global revenue.
Products that do not meet these requirements might not get or lose the CE mark, meaning they cannot be sold in the European market. However, products already placed on the EU market before December 11, 2027, don’t have to meet these rules, unless they undergo significant architectural and functional changes after that date.
Among other EU regulations that govern security, GDPR stands out. Created to protect personal data and ensure a privacy-first approach, it obliges any business that collects and processes users' data to do so in a transparent and secure way. Without strong data encryption, authentication, and user consent mechanisms, businesses can face fines of up to €20 million or 4% of global annual turnover.
In heavily regulated industries, security is the number one requirement for market approval.
In healthcare, for example, MDR (EU) and FDA (US) oversee the security of medical devices. Non-compliance can result in corrective actions, a complete product recall, or even criminal liability if the device harmed the patient.
For the automotive sector, there is UNECE WP.29, a cybersecurity regulation that requires manufacturers to implement specific actions to identify and mitigate cybersecurity risks across the entire vehicle lifecycle. Without it, vehicle manufacturers cannot operate in many global markets.
Security standards your embedded system must rely on
Although businesses are ready to adopt security standards, they sometimes don't know how. Often, there are too many nuances. And it's not always clear what to expect from a vendor. Here are the standards and frameworks that provide clear instructions on designing, developing, and maintaining secure systems.
ETSI EN 303 645
This EU standard provides the foundation for securing consumer devices connected to the Internet. At its core, it helps ensure data security throughout the system design process. For example, when developing embedded systems, our engineering team encrypts communication channels, securely stores sensitive data, and makes the system resilient to outages. To strengthen embedded software protection and safeguard users against emerging threats.
NIST
To support businesses of all sizes and industries, this framework provides recommendations based on best practices and standards for reducing cybersecurity risks. The development process for your product must follow secure coding practices with proper vulnerability management, using tools and components recommended by the framework.
ISO/IEC 27403
An internationally recognized standard provides a framework for establishing secure IoT systems in domestic settings. It covers requirements for device, data, and network security, as well as promoting user awareness. According to the standard, at the development level, our team incorporates secure boot mechanisms, authentication protocols, and ensures regular software and firmware updates to protect the device. We secure data with encryption, minimize data exposure, and safeguard networks through firewalls and secure protocols.
ISO 27001
Another international standard focusing on information security is ISO 27001. It relies on technological controls such as secure system configuration, access management, and encryption. Along with selected physical controls, these measures help to protect critical infrastructure directly within system design.
A big part of passing certifications and complying with regulations is having the right documentation in place. Our team handles it for our clients, keeping all records — from a detailed system overview and development process lifecycle to security controls, testing results, and maintenance actions. With all the necessary evidence in hand, businesses can easily pass certification audits and bring their products to market faster.
Qualities of embedded systems that affect security
While standards and frameworks help establish a strong security foundation, they do not eliminate all embedded system security threats. Designed to run continuously, perform specific tasks efficiently, and transmit data in real time, embedded systems face a range of security challenges because of these capabilities. Here are some of the key ones.
Longevity of devices
Devices that have been running for years with minimal updates may rely on outdated firmware and encryption algorithms, or obsolete hardware security components. For instance, two years ago, a cyberattack, Volt Typhoon, compromised thousands of devices, exploiting vulnerabilities in end-of-life routers, firewalls, and virtual private networks (VPNs). This case highlights how neglected devices can become entry points for attacks, so it is essential to plan timely firmware and end-of-life component updates.
Performance constraints
Many embedded devices, particularly in automotive and industrial settings, must operate in real time. Even a delay of a few milliseconds can cause physical malfunctions or operational failures. As most security measures are heavyweight, engineers used to choose real-time device performance over protection. Today, this is no longer the case — modern designs must balance performance requirements with strong security.
Most industry regulations mandate that manufacturers incorporate security into the system’s design by default. For example, under GDPR, non-compliance resulting in data breaches leads to fines or even restrictions on working with sensitive data.

Open-source software components
Software components in embedded systems frequently come from various vendors, often including open-source ones. While these components offer cost-efficiency, they may also have vulnerabilities that attackers can exploit. If a component is outdated or poorly maintained, it can become a weak link in the system, allowing attackers to execute remote code and compromise it.
Incorrect user authentication
In 2021, a Florida water treatment facility became a target of criminals, who accessed the SCADA control system through an outdated, shared password on a remote-access tool. Once inside, intruders attempted to increase the concentration of sodium hydroxide in the water, posing a threat to public health. This breach exposed a critical security issue: the system relied on shared credentials. Weak and shared, a lack of access control makes it easier for unauthorized users to bypass authentication by guessing passwords, stealing and using credentials, or changing existing passwords.
Input data validation
An attacker can compromise the system by simply entering an overly long string, a command disguised as a username, or malicious code. This way, they can access previously unseen information, leading to app crashes, resource exhaustion, and the leakage of confidential data. At the end, the company could face not only reputational damage but also a million-dollar fine.
Insecure communication protocols
Embedded systems frequently communicate using specialized protocols optimized for low power consumption or minimal bandwidth. Weak or poorly configured communication channels can allow attackers to manipulate transmitted data.
For example, in early 2025, a security audit revealed that more than 1 million medical IoT devices were exposing sensitive patient data online. Among the many reasons for leakage, one was the insecure, unencrypted communication modules. According to IBM’s 2025 Cost of a Data Breach Report, the average data breach in the healthcare now costs $7.42 million per incident, making it the most expensive sector for the fourteenth year in a row.
Common embedded systems security threats and warning signs
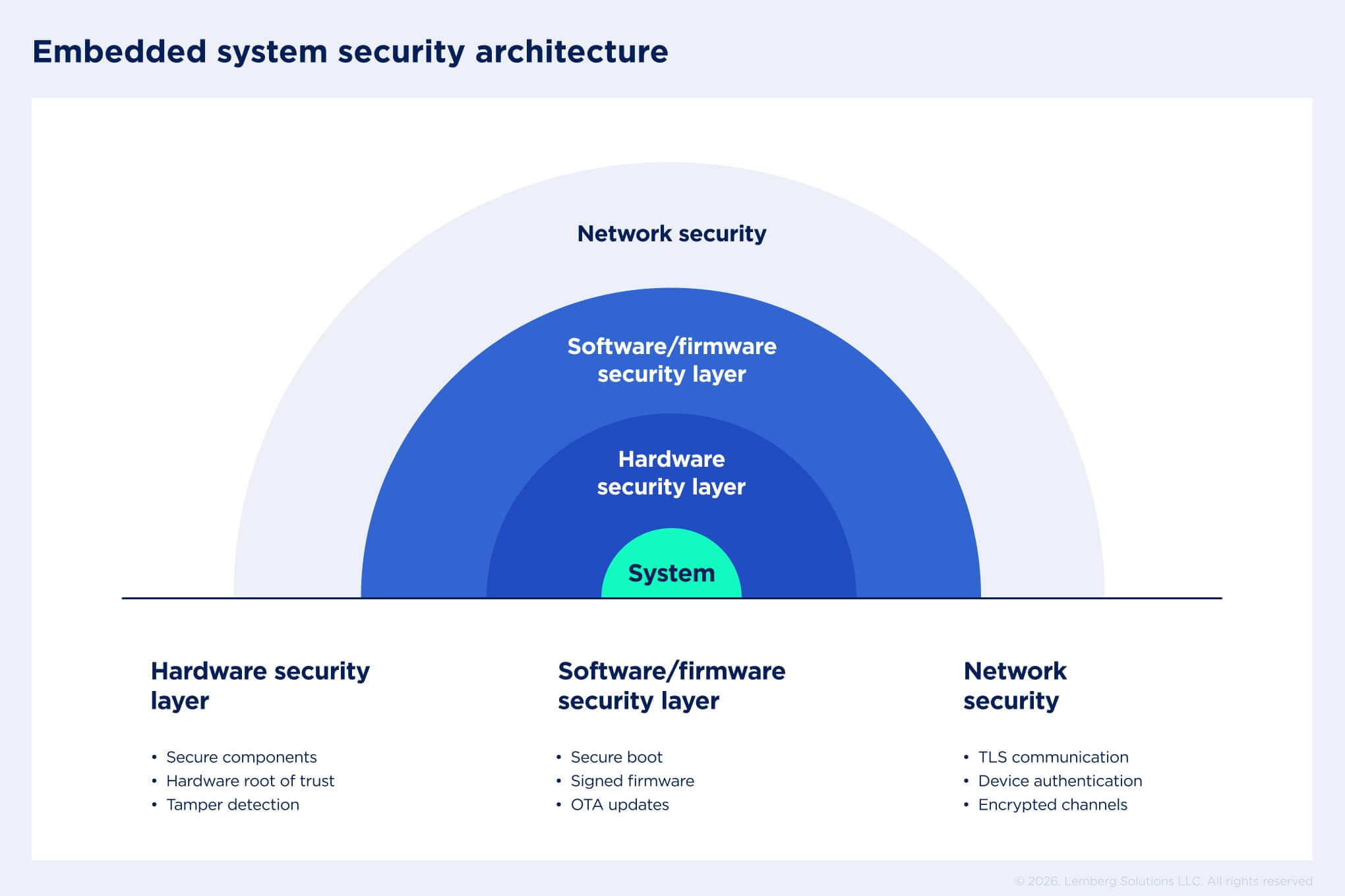
From hardware components to software and network layers, every part of a device can be a potential entry point for attackers.
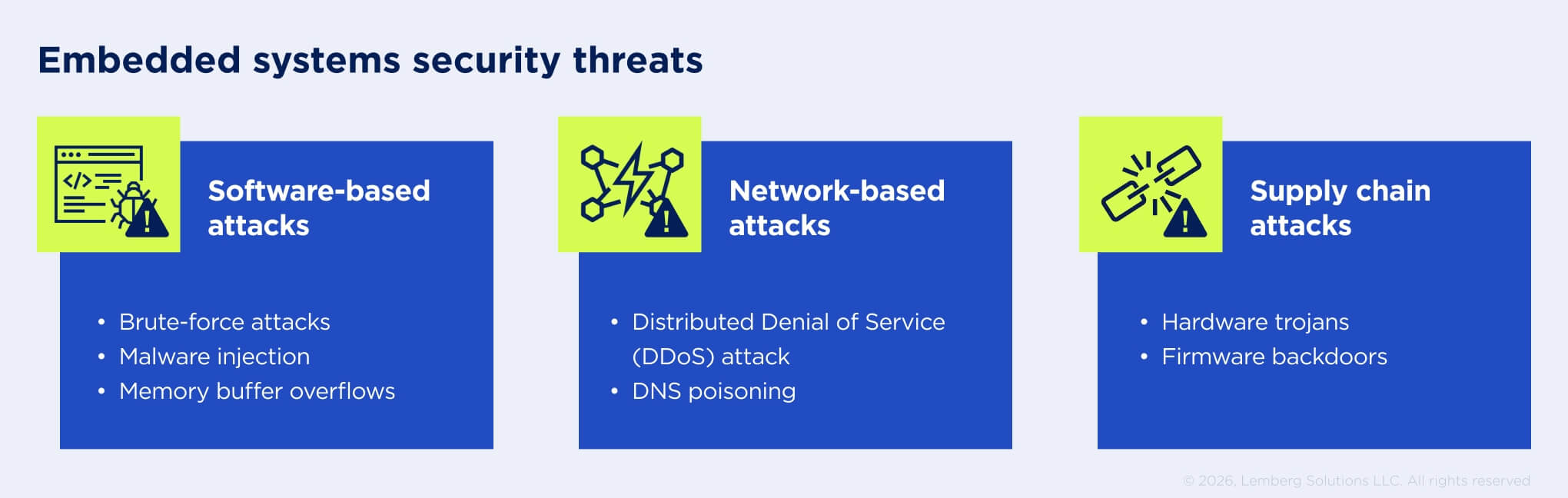
While the most common threats are illustrated in the image above, it’s important to understand that devices may appear to operate normally even when compromised. Recognizing subtle warning signs is critical to protect your system before damage occurs.
Unusual authentication activity
Repeated failed login attempts or authentication requests from unfamiliar locations may indicate that attackers are attempting to gain access. Similarly, successful logins occurring outside normal operational patterns, such as unexpected time zones or unusual accounts, can mean compromised credentials.
Behavioral changes
Embedded devices often operate in predictable patterns. Sudden changes from normal behavior can signal malicious activity. Examples include increased latency in real-time systems, unexpected processing delays, or unexplained spikes in power consumption and device temperature.
Suspicious network activity
Devices that begin sending unexpected outbound traffic, particularly to unknown servers, may have been compromised. In other cases, devices may also be co-opted into botnets, forwarding DNS queries or participating in distributed attacks unrelated to their intended function.
Best practices for securing embedded systems
Secure embedded systems start with design. At this stage, the architecture must incorporate the protection mechanisms outlined below and apply them across every layer of the system as it takes shape.
Data encryption
Protecting data in transit and at rest is a cornerstone of secure embedded systems. All data types collected, stored, and transferred within your embedded solution must be fully encrypted to prevent unauthorized access. This can be achieved through RSA-3072 or ECDSA algorithms, supported by key management practices, including hardware-based storage.
Network security
To reduce risk, system architecture must control how devices connect and communicate. And because most modern devices now communicate over networks, the key approaches include network segmentation and traffic control. This means separating IoT devices from devices that require local access to prevent attackers from using a single weak point to access the entire network. For better access control, tools such as firewalls, VPNs, and Network Access Control (NAC) filter traffic, allowing only authorized devices to join the network.
UI security
User interfaces can be another attack vector, so your UI security should include strong access control and hardening by disabling unnecessary interfaces. It also involves validating all user input to prevent injection attacks and isolating UI components to prevent malicious manipulation. On systems with graphical interfaces, users should be restricted from accessing the core operating system.
Secure boots & OTA updates
Security doesn’t end after a device is deployed. OTA updates make it possible to keep firmware up to date while ensuring each update is authenticated before installation. Secure boots add another layer of protection by establishing a root of trust, allowing only trusted code to run and preventing rollback to vulnerable versions.
Constant security updates
Establishing an embedded security policy once is not sufficient. Along with regular firmware and hardware component updates, the methods for safeguarding your product should also be continuously reviewed and upgraded to meet new standards. For example, vulnerability tests identify potential security risks, which helps to be aware of emerging issues you may face.
Secure hardware environment
When measuring the security of your embedded system, it is important to consider the possibilities of hardware tampering and enable early detection of attempts at unauthorized access to your equipment. Within this context, secure peripheral assignment is a key element, as it ensures that sensitive sensors or peripherals are only accessible from the secure trusted domain.
Secure supply chain management
Embedded systems security also depends on the integrity of the hardware and software supply chain. Businesses must ensure that all components they use for development originate from trusted sources and have not been modified during manufacturing or distribution.
At the same time, security doesn’t end at the design stage. Effective threat response mechanisms are essential for detecting, containing, and resolving issues quickly while minimizing potential damage. For businesses with mature infrastructure, working with embedded security experts can help identify gaps through system audits and define strategies that strengthen security across the entire architecture.

Embedded system vulnerability management lifecycle
With the rise of AI, security threats have become smarter than ever. And the key to feeling confident in this reality is to implement vulnerability management. This approach helps quickly detect and address potential vulnerabilities before they impact your system. In collaboration with your tech vendor, you can manage this process by following the four key steps.
- Vulnerability detection
To understand which part of your system is targeted, start with SBOM analysis, which will provide a complete list of the system components. Then, you can use specialized analysis tools to scan your system against public vulnerability databases. It will allow you to identify potential threats that could affect your system. - Analysis and prioritization
Not every vulnerability poses the same level of threat to the system. Therefore, your team must assess the potential consequences of each vulnerability — what impact they will have on your business and users. Focus on those vulnerabilities that are too critical for your system and must be addressed first; then, filter out vulnerabilities with minimal or no impact. - Remediation
Once prioritized, you will have a list of all the issues. At this stage, you can push firmware updates or apply specific patches. Sometimes, when immediate fixes are not possible, you can use temporary mitigation strategies to ensure that the danger is effectively neutralized. - Reporting
The final stage of the cycle ensures that vulnerability remediation is properly verified and documented, confirming all updates have been successfully installed. For industries that require compliance with security standards, this is particularly important. Reporting allows auditors to understand the current security state of your embedded system — what has been fixed and what still needs to be changed.
Balancing embedded security with project budget: three main advices
While most embedded devices must have a secure mechanism in place, there is a significant difference between consumer devices and those used in heavily regulated industries. If meeting baseline security standards is sufficient for consumer devices, it is not enough for high-risk devices. They must have a security-by-design architecture from day one to pass all industry certifications.
The most expensive approach is trying to add security after the device is fully developed. Typically, it requires more architectural changes, firmware rewrites, and additional testing, which leads to budget overhead. Below are several pieces of advice that can help balance security needs with budget constraints.
#1 Prioritize threats
Rather than implementing every possible security feature, it is better to start with threat modeling. This process allows you to monitor the attacker's typical actions and identify potential vulnerabilities in your system.
Without threat modelling, teams often over-engineer security by applying complex protections, unnecessarily increasing costs and complexity. Before the development process starts, industry and market-specific security requirements must be considered. In practice, this means focusing on the most relevant protection measures to deliver the greatest security impact without unnecessary cost or complexity.
#2 Do not overengineer — use built-in hardware capabilities
Many modern microcontrollers include built-in security capabilities. Today’s MCUs feature hardware-based encryption, secure boot, tamper detection, and trusted execution environments. Moreover, some are certified to standards such as PSA Level 3 and FIPS 140-2.
What we recommend is to focus on using these internal hardware capabilities to the fullest instead of adding more security chips or upgrading to a more powerful MCU. Such an approach allows for ensuring strong system security while maintaining budget efficiency and reducing system complexity.
#3 Test the system’s security smarter
Security testing does not always require expensive platforms and tools. Now, most open-source tools have reached a considerable level of maturity, allowing more thorough testing of embedded systems.
In our practice, we combine established, industry-proven tools with expert analysis. This ensures accurate interpretation of results and minimizes false positives. As a result, our engineering team can identify and resolve risks early without increasing the project’s budget.

Distinct embedded security lifecycle workflows: end-to-end Lemberg Solutions’ approach
The engineering team at Lemberg Solutions follows a secure-by-design philosophy — our workflow ensures that risks are identified early and mitigated continuously. Also, as an ISO 27001-certified vendor, we enforce strict information security management: only authorized engineers and team members have access to project documentation.
Here’s how our end-to-end services ensure strong protection for embedded systems:
Requirements evaluation
The development lifecycle begins with identifying the assets that require protection, such as sensitive user data, intellectual property, device credentials, or operational logic. At this stage, the team evaluates the potential threats. By prioritizing these risks early, it can focus its efforts on implementing the protections that will provide the greatest value.
Embedded system architecture and hardware selection
During the design phase, we develop the system architecture, addressing the threats identified during the requirements evaluation. With your specific project needs in mind, our team selects hardware and software components, taking into account their built-in security mechanisms to strengthen the device's overall resilience.
Secure development & testing
During development, we apply industry-proven security practices to minimize vulnerabilities. Our developers use analysis tools to scan code for weaknesses and follow secure coding standards. This stage also includes the mechanisms for data encryption and the development of the secure update mechanism. All third-party libraries are documented in a Software Bill of Materials (SBOM) to track potential vulnerabilities in open-source components. Also, to protect embedded and IoT systems, we incorporate Public Key Infrastructure (PKI) as a core component of the security architecture for device authentication, encrypted communication, and secure firmware updates.
Aligned with industry standards for regulated sectors such as medical devices, automotive, and industrial systems, we apply the V-Model development methodology. This strategy allows testing and validating the system’s functionality at each stage of product development.
Lifecycle management and OTA updates
Once devices are deployed, the focus shifts to maintenance and continuous monitoring. We observe the device behavior for anomalies that could signal unauthorized access or attempted compromise. In the event of a security breach, our workflow includes typical vulnerability management actions to normalize the situation. Also, embedded systems receive OTA updates to deliver firmware updates or address newly discovered threats.
Compliance and certification support
Depending on the industry, clients often require additional support to prepare for certification audits. On our side, we provide the documentation, test results, and architectural evidence required to obtain certifications for market entry. This is done in accordance with relevant industry standards, such as ISO 21434 for automotive, IEC 62443 for industrial systems, and ISO 13485 or IEC 62304 for healthcare and medical devices.